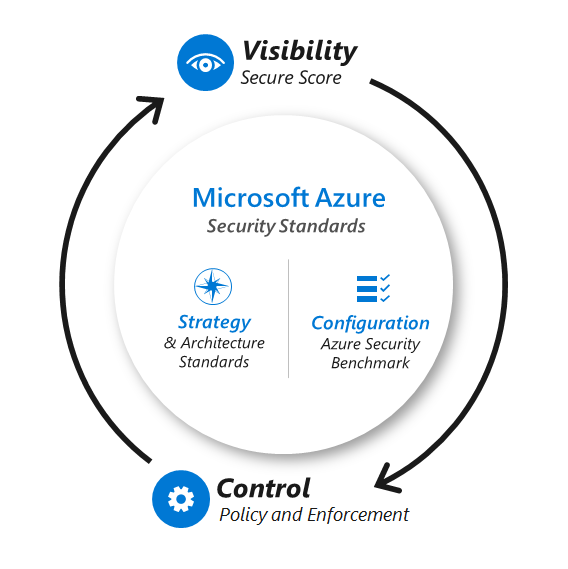
Azure Cloud App Security provides a comprehensive, intelligent security solution that brings visibility, real-time control, and security to your cloud applications. There is no denying how significant the cloud has an essential tool for businesses to optimize their operations and increase efficiency. Cloud apps are a great standard to deliver software products, services, and applications to employees while reducing costs.
However, as the number of individuals who access business data through cloud apps expands, it’s crucial to maintain your devices safe. SaaS apps are being used by more and more businesses, not just to cut costs but also to gain competitive advantages like accelerated time to market and enhanced collaboration. However, your workers do even if your business hasn’t used cloud software. The fast transition to cloud apps may leave you concerned about storing corporate data in the cloud apps.
Data flows to many places, including mobile device, applications, cloud services, and on-site sites. Achieving visibility and control over data in cloud apps is crucial, given the rise in cybersecurity assaults and the need to comply with important legislation.
How Azure App Security Can Benefit Microsoft’s Cloud Strategy
The Azure Cloud App Security environment enables businesses to manage their digital assets from a single, secure location. In addition, the Service allows organizations to manage their applications and data across multiple platforms, including Windows Azure, Office 365, and SharePoint online accounts.
Microsoft’s cloud strategy has been gaining momentum recently as many customers see it as a capabilities to save money while continuing with the business. This is especially important for smaller companies that may not have the resources or workforce to invest in traditional IT infrastructure.
Businesses are taking advantage of Microsoft cloud app security because they can be deployed quickly and easily without concern about security or reliability. They may also be scaled up or down to meet your needs without impacting performance or other aspects of their system operations. Microsoft has created a secure, reliable, and cost-effective environment for businesses looking for feature to benefit from cloud computing without sacrificing their existing systems’ functionality or capabilities.”

Getting Started with Claims-Based Identity and Access Management
Suppose you’re managing your identity and access management in Azure. In that case, you’ll find that a claims-based identity is a two-factor authentication and access management approach designed to work across the full range of Microsoft Cloud App Security services. Claims-based identity is a standard of authenticating users, controlling access to resources, and verifying that the user access is authorized to standard them.
In addition to reducing infrastructure dependencies, claims-based identity provides a consistent approach to two-factor authentication that you can apply across the full range of Azure Cloud App Security services. One key benefit of claims-based identity is that it reduces infrastructure dependencies: Applications secured by claims-based identification may be hosted without any adjustments on-premises or in the cloud.
Developers targeting Azure Cloud App Security can use the same tools and services available to their on-premises counterparts, which means they don’t have to learn new ones—they get access to more features!
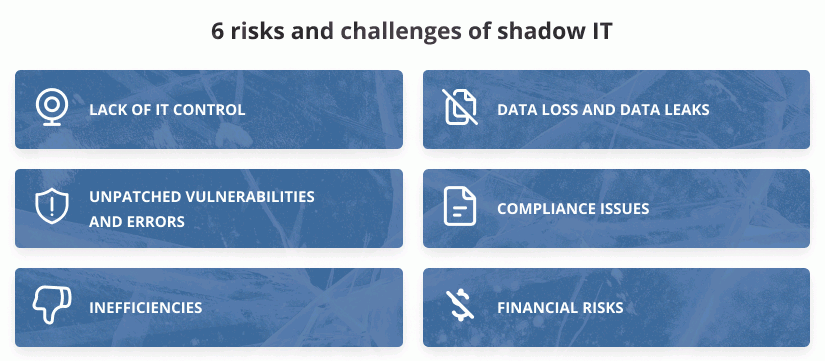
How Cloud App Security Detects The Risk Of Cloud Apps And Tackles Shadow IT
The risk of cloud apps and Shadow IT is a growing concern for organizations worldwide. Azure Cloud App Security can help you quickly spot abnormalities by detecting ongoing risks and providing information on user experience, unusual use patterns, upload/download activity, and transactions. For instance, Microsoft cloud app security notifies you when a user transfers a single sign significant amount of data to a dangerous app, allowing you to take the necessary action immediately. In addition, anonymization of data and logs helps to safeguard user privacy.
Cloud App Security recognizes over 15,000 cloud apps, and no agents are needed. It also assesses the danger posed by these applications using more than 60 criteria, such as support for Multi-factor authentication or two-factor authentication methods, IP address restrictions, and regulatory compliance. You can use the risk score to choose whether to approve the app. The first step in understanding Shadow IT is locating cloud applications on your network and obtaining insight into them.
How Cloud App Security Helps You Protect Data in the Public Cloud and Control Risk
With cloud app security, you can control data in the public cloud and protect your organization’s most sensitive information. Granular control policies and effective single-click remedies, such as document quarantine and sharing limitations, are made possible by Microsoft cloud app security.
You may apply pre-built policies or modify them to Microsoft or third-party programs such as Box, Dropbox, Salesforce, and others. For example, Azure Cloud App Security may scan and categorize files in the cloud, and You can apply Azure Information Protection labels for protection, including encryption.
Regulatory requirements, including the Payment Card Industry, Health Insurance Accountability and Portability Act, Sarbanes-Oxley, and General Data Protection Regulations, are supported by Cloud App Security on your compliance path. In addition, apps from Microsoft or other suppliers, such as Box, Dropbox, Salesforce, and more, are subject to the policies set out by Cloud App Security. Cloud App Security assists you in further controlling and protecting important files through policies and governance and considers compliance with legislation into the risk assessment score for each app.
Microsoft Cloud App Security Threat Detection & Ransomware Protection
Cloud App Security is a single sign designed to protect your SaaS applications, so you can focus on what you do best: providing new and innovative services to your customers. When an anomaly is identified in cloud usage, Microsoft cloud app security learns how users interact with each SaaS app and assesses the risks in each transaction. It does this through behavioral analytics that generates a model that predicts potential risks based on historical data.
These can include repeated unsuccessful login attempts that could indicate a brute-force assault, simultaneous logins from two continents, or the rapid download of terabytes of data. In addition, a built-in policy template for ransomware detection is available through Cloud App Security threat detection, for instance, by looking for unusual file extensions.
Using this template, you may set governance actions to suspend questionable users and stop future file encryption. By connecting your SIEM and DLP solutions, Microsoft cloud app security aids in the preservation of your established process. In addition, it makes it possible to have a uniform policy for both on-premises and cloud environments while automating security controls to safeguard your cloud apps better!
Benefits Of Security Threats And Mitigation In Microsoft Azure Cloud App Security
While the point of a web application is to provide a service, it must also be secure. A cloud-based web service’s security environment differs single sign from traditional hosted web services in mitigating tools and technologies, making protecting your application more complex.
Appendix B contains a security threat matrix specific to Azure Cloud App Security, which can help identify an application’s most critical security threats. In addition to understanding your applications’ threats, it’s essential to know how they are mitigated. The security controls available in Azure Cloud App Security provide several standard to mitigate these threats and ensure that your app is secure—from defenses against known vulnerabilities (such as Cross-Site Scripting or SQL injection).
To controls that help prevent users from accessing unauthorized resources on your servers (such as Azure Active Directory) or even through Azure’s cloud data center security! Security threats might be of any size or kind, so you must understand what they might be so that you can adequately protect yourself against them.
How does Azure protect confidential data in Cloud App Security?
Azure Cloud App Security provides a secure, encrypted storage solution for your confidential data. However, it does not support Data Protection API (DPAPI)-like the persistence of private data in Azure Cloud App Security.
If a service must encrypt confidential data at rest within Windows Azure Storage, then it needs to encrypt that data offsite and before uploading the encrypted payload to blob storage. You can do this quickly with an AES key generated on a client machine or elsewhere within the enterprise. Also, developers should not upload the key or any keying material to Azure Cloud App Security.
Instead, upload them through the Developer Portal and access them via thumbprint references in the Service Configuration. Cloud App Security will not only store these certificates encrypted at all times but also securely provision them into the certificate stores of the Service’s web roles upon boot. Developers should not attempt to store certificates alone as these actions would constitute re-inventing protection already supplied by the platform.
EPC Group Offers Full Suite of Microsoft Azure Cloud Consulting Services
Microsoft Azure Cloud App Security provides much-needed visibility into the cloud apps that are used by your employees and helps you implement intelligent security policies such as using two-factor authentication. It helps customers gain visibility into the use of cloud apps for their employees and enables administrators to enforce policies on managed and unmanaged applications across clouds based on risk. Regarding integrating with existing security systems, Microsoft Cloud App Security makes adopting a mobile device workforce easier without slowing down IT. It also provides strong password two-factor authentication through its Active Directory integration, which ensures a seamless experience across all devices and platforms.
EPC Group has worked in the Microsoft Azure consulting realm for over four years and is usually regarded as the industry leader. To assist our clients in staying one step ahead of their rivals, we strive hard to remain experts in our industry. If you’ve already wanted to learn about what EPC Group can do for your business.