Microsoft Defender for IoT, also known as Azure Defender for IoT is a unified security solution that is designed for the identification of IoT/OT devices, their vulnerabilities, and other threats. It enables the user organization to secure their entire IoT/OT environment. The use of this solution is widespread and it can prove to be beneficial for almost all user organizations in every industrial sector. In this blog post, we will discuss Azure Defender For IoT Pricing and features in detail.

Azure Defender For IoT Pricing And Features
Azure Defender for IoT pricing structure:
The IoT security service by Microsoft is a security solution designed to identify the weak spots across the cloud configuration used by the user organizations. In addition to this, the solution raises the cybersecurity standard of the user companies along with protecting workloads across multiple cloud platforms and hybrid environments, against multistage attacks.
The Azure Defender for IoT pricing structure consists of features that are now collectively known as Defender for IoT. These features deliver security for Azure-connected environments. The features under this service can be distinctly categorized into two sets of capabilities, which can be stated as follows:-
- Agentless monitoring and
- Security monitoring for new devices that are provisioned through the Azure IoT Hub.

The pricing structures of these categories can be illustrated in the following manner:-
- Agentless Monitoring: The agentless monitoring features within the Azure Defender for IoT is completely free for the first 1,000 committed devices for the first 30 days. After this limit is exceeded, the customers are automatically charged according to a pricing structure that is given below –
| Solution | Price |
| Defender for IoT agentless security on-premises | $140/month per 100 monitored devices, based on commitment |
| $1,680/per 100 devices per 1-year commitment |
But, it is to be noted that there is no cost for ingesting Defender for IoT alerts and incidents into Microsoft Sentinel.
- Security monitoring for new devices that are provisioned through the IoT Hub: The Defender for IoT also provides device layer security for new devices that are provisioned and managed through the IoT Hub. These include the ones that have the Defender for IoT security agent installed in them. Such built-in IoT/OT security capabilities are free of any charges for the first 30 days. Any use of these features beyond the limited period is automatically charged according to the table given below –
| Solution | Price |
| Defender for IoT for devices managed by IoT Hub – by device | $0.001/month |
| Defender for IoT for devices managed by IoT Hub – by messages | $0.20/25k transactions |
Essential features of the Azure Defender for IoT and OT:
The essential features under Azure Defender for IoT pricing structure can be enumerated in the following manner:-
- Apart from the traditional network security and monitoring tools, it has the potential of providing agentless security solutions which can provide visibility and security for all networks.
- The automatic device discovery feature helps in gaining a complete inventory of all the IoT/OT devices and their other details.
- Risks and vulnerabilities can be identified clearly with the help of this solution along with identifying the changes to devise configurations.
- Unauthorized activities and threats can also be identified by the Azure Defender for IoT.
- Unified security management is also one of the unique features of the solutions which are achieved after the integration with Microsoft Sentinel that provides the user with a comprehensive view of the whole organization.
Agentless monitoring and Network-layer security: An understanding
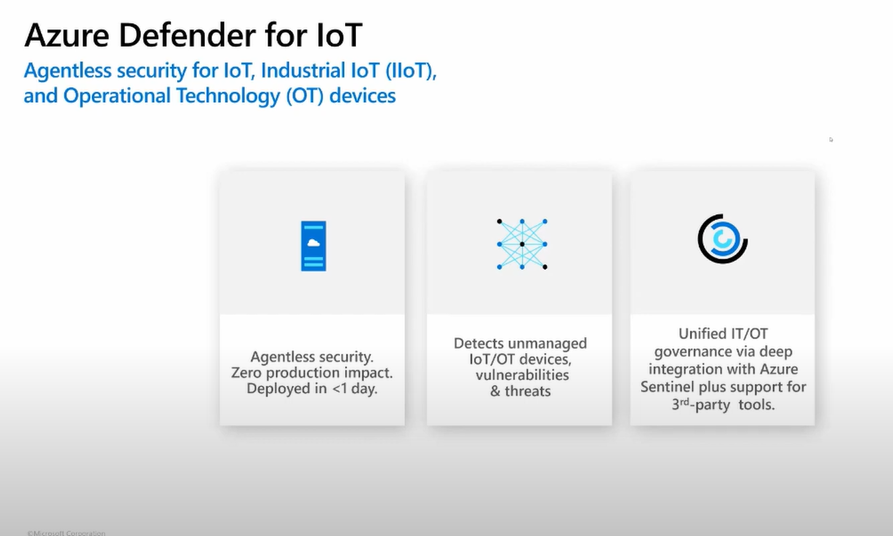
The agentless monitoring technique is also known as passive monitoring provides the necessary agentless security system required by user organizations in contemporary times. This technique provides a safe and complete inventory of all the IoT/OT assets with zero impact on IoT/OT performance. The user companies can also analyze diverse and proprietary industrial protocols to visualize the IoT/OT network topology and see the other communication pathways.
This information can later be used to accelerate network segmentation and zero trust initiatives. The feature is specifically advantageous for manufacturers as it gives equipment details such as manufacturer, device type, serial number, firmware level, and backplane layouts. Quick identification of the root causes of operational issues such as misconfigured devices and networks is also possible.
Benefits of integrating Azure Defender for IoT:
The Azure Defender for IoT can be integrated with the Microsoft Sentinel which turns out to be quite beneficial for the user organizations. This feature provides the user with a sharp view across all the IT/OT boundaries with Interoperability that is provided within IoT/OT – specific SOAR playbooks. These playbooks can help in automating responses.
Along with this, the machine learning and threat intelligence capacities from trillions of signals collected across the global ecosystem of Microsoft can be augmented by IoT/OT-specific intelligence collection research team. The user organizations can also prevent attacks through extended detection and response from Microsoft 365 Defender. Finally, the user is also provided with Interoperability with other SOC tools like Splunk, IBM QRadar, and ServiceNow.
Behavioral analytics: Meaning and its implications

Behavioral analytics is one of the unique features of the Azure Defender for IoT. This allows the user organization to monitor internal activities like anomalous or unauthorized activity using IoT/IoT aware behavioral analytics and threat intelligence capabilities. The Zero Trust Security can be strengthened by instantaneously detecting unauthorized remote access and unauthorized or compromised devices.
In addition to this, the real-time alerts can be rapidly tracked through historical network traffic analysis. Also, modern-day threats like zero-day malware and living off-the-land tactics can be identified.
Benefits of using Azure Defender IoT for new initiatives:
The benefits of using Azure Defender IoT for new IoT initiatives can be reaped by the manufacturers and solution operators. These facilities can be categorized in the following manner:-
Built-in IoT/OT security capabilities
For new IoT projects – The Azure IoT security strategy involves the capacity to help protect new IoT devices and other Azure IoT projects from the first day through the deployment of the Defender for IoT security micro-agents. This reduces risks with real-time security passive monitoring across standard IoT operating systems. In addition to this, the feature also supports compliance and continuous visibility into the user organization’s IoT security, directly from the endpoint. The continuous threat intelligence of Microsoft can detect the evolution of threats. Also, custom alerts can be created for defining the most critical threats to the environment of the user organization.
Protecting IoT devices with minimal impact on the endpoint
This feature allows the user organization to deploy endpoint security with minimal impact on the IoT devices. It is possible because the Defender for IoT security micro-agent has a small footprint and consists of no OS kernel dependencies. In addition to this, the user organizations can deploy using the distribution model that is designed to work best for their devices along with modifying source code to further customize the agent that is required for the specific needs. Micro-agents are made available for the standard IoT operating systems, including Linux and Azure RTOS.
Securing the Azure IoT projects from edge to cloud

The Defender for IoT comes with solutions like Azure IoT Edge and Azure RTOS that can be used in securing the projects from edge to cloud along with security recommendations and alerts directly in Azure IoT Hub. Additionally, cloud security posture management can be used to protect the organizational workloads that use extended detection and response from Microsoft Defender for Cloud. Finally, the IoT security alerts can be fed into the entire view of the enterprise by connecting to Microsoft Sentinel.
EPC Group Azure Consultation: An Azure Defender for IoT perspective
The EPCGroup is one of the organizations that are capable of providing a comprehensive Azure IoT security strategy that is equipped with threat intelligence to the critical infrastructure organizations typically use in the present day. We employ a group of experts that work consistently towards helping their clients to navigate across the cloud and adhere to the industrial protocols of security and compliance.
The EPC Group has more than two decades of experience in customizing training programs that cater to the specific needs of the user organizations. In addition to this, the company is a gold-certified partner of Microsoft which implies that this is the best consultation partner for user companies during their implementation process related to IoT / OT devices.
The company also concentrates on keeping a check on the financial aspects of using the cloud platform including its cost of ownership. The company also provides round-the-clock customer support to assist the end-user organizations in their process of deep integration.
Conclusion:
In conclusion, it can be said that the convergence of IT operational technology and the Internet Of Things has resulted in a complex and disconnected ecosystem in the digital platform. This ecosystem poses troubles for important infrastructure providers in the sphere of integration and security. The issues arise because the existing third-party IT security tools are not suited for deep integration with the IoT and OT environments while several IoT devices cannot be configured for security.
The Microsoft Defender for IoT pricing and features combines Microsoft’s operational technology and threat intelligence capabilities in helping companies gain clear visibility into their data and network. In addition to this, the organizations will be successful in continuous threat monitoring which will help in increasing the resilience of their operating systems.